The Vulnerability Exchange Protocol: How to Open Up After a Breakup Without Getting Destroyed
Introduction
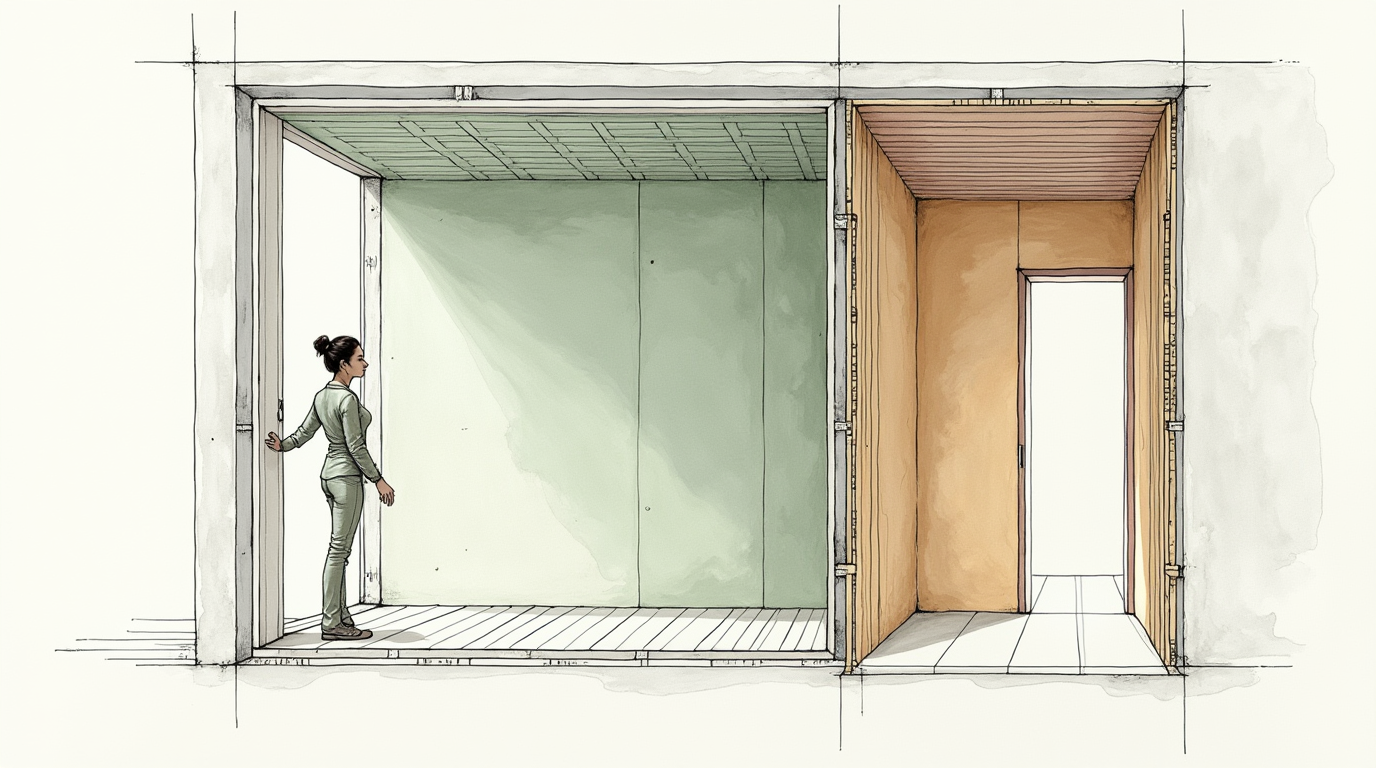
Someone told you to "just be vulnerable" and you wanted to throw something at them.You know why. The last time you were vulnerable — fully, honestly open with another person — it was used against you. Maybe not dramatically. Maybe it was the slow leak: sharing your fears and watching them become ammunition in arguments. Telling someone what hurt you and watching them do that exact thing. Opening your chest and handing someone the map to every weak point you have.So now your system is locked. You can function. You can socialize. You can even date. But the door that lets someone actually reach you? Sealed. And every self-help article telling you to "embrace vulnerability" feels like asking you to walk back into the building that just collapsed on you.Quick Answer: Vulnerability after a breakup isn't about being braver or more open. It's about having a structured protocol for emotional disclosure that protects you while you rebuild the capacity for connection. Unstructured vulnerability after trust violation is retraumatization, not courage.I call this The Vulnerability Exchange Protocol because vulnerability should function like a negotiation, not a confession. You disclose at a pace and depth that matches the trust evidence the other person has actually earned — not the trust you hope they deserve.After years of working with women who either locked down completely or overcorrected by flooding new relationships with premature emotional depth, I've observed that the problem isn't willingness to be vulnerable. It's that nobody teaches the mechanics. When to open up. How much. With whom. And critically — how to recognize when your vulnerability is being received versus when it's being collected.This isn't about being brave. It's about being strategic. Let me walk you through the system.
The Exposure Response: Why Vulnerability Feels Dangerous After a Breakup
Your resistance to vulnerability isn't a character deficiency. It's your nervous system running a program I call The Exposure Response — a protective shutdown that activates after trust violation to prevent repeated injury.
Here's how it works neurologically: during your relationship, your brain built oxytocin circuits around your partner. Oxytocin — the bonding hormone — creates a sensation of safety during emotional disclosure. When you shared something personal and your partner received it with care, your brain released oxytocin. Over time, vulnerability became linked to reward: share something real, receive connection.
When that partner violated your trust — whether through betrayal, dismissal, weaponization of your disclosures, or abandonment — the circuit didn't just break. It reversed. Your brain now associates vulnerability with threat instead of reward. The same neural pathways that used to say "opening up equals safety" now say "opening up equals danger."
This is The Exposure Response: your nervous system treating emotional openness as a threat equivalent to physical exposure. The racing heart when someone asks how you really feel. The deflection when a conversation gets too personal. The instinct to perform "fine" instead of sharing actual experience. These aren't personality traits. They're protective reflexes.
I see three common Exposure Response patterns in my practice:
Pattern 1: The Fortress You lock everything down. You're warm, social, even funny — but nobody gets past the surface. When someone tries to go deeper, you redirect the conversation, make a joke, or offer advice instead of disclosure. You'll listen to anyone else's pain all day long, but yours stays sealed.
The cost: Fortress builders create relationships that feel warm but emotionally flat. Partners eventually notice they know nothing real about you, which creates the distance you were trying to prevent.
Pattern 2: The Flood The opposite extreme. You overcorrect from your previous guardedness by sharing everything, too fast, with people who haven't earned that level of access. First date confessionals. Deep trauma disclosure within weeks. The logic feels sound: "I'm being open this time. I'm doing the brave thing."
The cost: Flooding creates false intimacy that collapses when the other person can't hold the weight of what you've shared. It also hands unvetted people detailed maps to your vulnerabilities — which is exactly how the last relationship became dangerous.
Pattern 3: The Oscillator You swing between Fortress and Flood, sometimes within the same conversation. One moment you're sharing something deeply personal, the next you're withdrawing and regretting it. You feel exposed after any disclosure, even appropriate ones, and spend hours analyzing whether you said too much.
The cost: Oscillation creates confusion for the people around you and shame cycles for you. The inconsistency makes it hard to build trust because neither you nor the other person knows which version of your openness to expect.
The critical insight about The Exposure Response: it's not the problem. It's a symptom. The problem is that your vulnerability system has no structure. Without a protocol for when, how much, and with whom to open up, your nervous system defaults to one of these three patterns because it has no other framework to follow.
That's what The Vulnerability Exchange Protocol provides — not a command to "be brave" but a structure that gives your nervous system the guardrails it needs to open gradually, safely, and in proportion to the trust that's actually been established.
Key Insights: - The Exposure Response: nervous system treats emotional openness as threat after trust violation, reversing vulnerability-reward circuits - Three common patterns: Fortress (total lockdown), Flood (premature overcorrection), Oscillator (swing between both) - The response isn't a character deficiency — it's a protective reflex operating without structure - Unstructured vulnerability after trust violation defaults to one of three problematic patterns - The solution isn't more courage — it's a protocol that gives the nervous system graduated guardrails
Put It Into Practice: - Identify which Exposure Response pattern you default to: Fortress, Flood, or Oscillator - Notice when The Exposure Response activates: racing heart, deflection, performing 'fine' — these are protective reflexes, not personality - Don't fight the response. It's protecting you. The goal is to give it a better operating system, not to override it
Key Points
- The Exposure Response: vulnerability-reward circuits reverse after trust violation, linking openness to threat
- Three patterns: Fortress (lockdown, surface-only warmth), Flood (premature deep disclosure), Oscillator (swing between both)
- Resistance to vulnerability is a protective reflex, not a character flaw
- Without structure, the nervous system defaults to one of three problematic patterns
- The solution is a graduated protocol, not a command to be braver
Practical Insights
- Identify your default Exposure Response: Fortress, Flood, or Oscillator — each requires different correction
- Notice when the response activates (racing heart, deflection, performing 'fine') — these are data, not failings
- Don't override the protective response — give it a better framework to operate within

The Vulnerability Gradient: Five Levels from Surface to Core
The advice to "be vulnerable" fails because it treats vulnerability as binary — either you're open or you're closed. In reality, vulnerability operates on a gradient with five distinct levels, and the level you share should be calibrated to the trust the other person has demonstrated through behavior, not promised through words.
I developed The Vulnerability Gradient as a diagnostic tool because most women I work with don't have a vulnerability problem — they have a calibration problem. They're either sharing Level 4 depth with Level 1 trust (Flood pattern), or restricting everything to Level 1 regardless of how much trust has been established (Fortress pattern).
Level 1: Social Surface What you share: Preferences, opinions, daily experiences. "I love this restaurant." "Work was exhausting today." "I've been watching that show." Trust required: None. This is public information. Purpose: Establishing baseline compatibility and communication comfort. Risk: Virtually zero.
Level 2: Personal Context What you share: Background information, values, general life experiences. "I moved here after college." "Family is important to me." "I went through a rough patch a few years ago." Trust required: Demonstrated consistency — they follow through on plans, communicate reliably, show basic respect. Purpose: Testing whether they engage with personal information appropriately. Risk: Low. This is information a coworker or casual friend might know.
Level 3: Emotional Honesty What you share: Current feelings, needs, preferences that create vulnerability. "I feel anxious when plans change last minute." "I need more reassurance than average right now." "That comment landed harder than you probably intended." Trust required: Demonstrated respect for your boundaries AND evidence that previous disclosures (Levels 1-2) were received without judgment, dismissal, or weaponization. Purpose: Testing whether they can hold emotional information without distorting it. Risk: Moderate. This is where exploitation potential begins.
Level 4: Core Wounds What you share: Deep fears, past trauma details, attachment patterns, things you're ashamed of. "My ex cheated and I still feel broken." "I have abandonment patterns from childhood." "I don't trust my own judgment about people anymore." Trust required: Significant demonstrated trustworthiness across multiple situations over weeks or months. They've handled Level 3 disclosures with consistent care. They've repaired mistakes. They've shown they don't use information as leverage. Purpose: Building genuine intimacy through reciprocal deep disclosure. Risk: High. This is the information that can be weaponized in conflict.
Level 5: Unprotected Depth What you share: The things you've never told anyone, or told very few people. The disclosure that would make you feel destroyed if it were used against you. Trust required: Years of demonstrated trustworthiness, not months. This level is reserved for people who have been tested across multiple life circumstances and have consistently chosen your wellbeing. Purpose: The deepest intimacy. Available to very few people in a lifetime. Risk: Maximum. Only appropriate with thoroughly vetted, long-term trusted individuals.
The Gradient Rule: Never share a level higher than the trust evidence supports.
This sounds obvious, but it's the rule that almost everyone breaks, especially after a breakup. When you're lonely, when someone seems to understand you, when the connection feels electric — your brain pushes you to share at Level 4 when you're still at Level 1 trust. The connection feels deep. It's actually just fast.
I tell my clients: depth without evidence is exposure, not intimacy. Real intimacy is built by matching your vulnerability level to the trust the other person has earned through consistent behavior over time.
The Graduation Markers — How to Know Someone Has Earned the Next Level:
Level 1 to Level 2: They show up consistently. Plans kept. Communication reliable. Basic respect demonstrated.
Level 2 to Level 3: They've received personal information without judgment or dismissal. They reference things you've shared in ways that show they listened. They don't use your information competitively.
Level 3 to Level 4: They've handled your emotional honesty with care. When they've hurt you (even accidentally), they've repaired it. They've shared their own Level 3 material reciprocally. They haven't punished you for having needs.
Level 4 to Level 5: They've been tested by time and circumstances. They've held Level 4 information through conflict without weaponizing it. They've demonstrated consistent trustworthiness across months, not weeks.
Key Insights: - The Vulnerability Gradient: five distinct levels from social surface to unprotected depth - Each level requires demonstrated trust evidence, not promised trust - The Gradient Rule: never share a level higher than the trust evidence supports - Post-breakup vulnerability problems are usually calibration problems — wrong depth for the trust level - Graduation Markers: specific behavioral evidence required before progressing to the next level
Put It Into Practice: - Identify what level you typically share at with new people — and what level of trust they've actually demonstrated - If you're a Flood pattern: consciously restrict to Level 2 for the first month of any new connection - If you're a Fortress pattern: practice sharing at Level 2 with people who've demonstrated Level 2 trust — your system needs graduated practice, not a grand gesture - Track Graduation Markers in Untangle Your Thoughts — when evidence accumulates on paper, your nervous system has something to reference besides fear
Key Points
- Five vulnerability levels: Social Surface, Personal Context, Emotional Honesty, Core Wounds, Unprotected Depth
- Each level requires specific behavioral trust evidence, not verbal promises
- The Gradient Rule: never share a level higher than demonstrated trust supports
- Post-breakup vulnerability problems are calibration issues — wrong depth for the actual trust level
- Graduation Markers: specific observable behaviors that signal readiness for next level
Practical Insights
- Identify your typical sharing level with new people vs the trust actually demonstrated — the gap reveals your calibration error
- Flood pattern correction: restrict to Level 2 for the first month of any new connection
- Fortress pattern correction: practice Level 2 sharing with people who've earned Level 2 trust — start small
- Track Graduation Markers in Untangle Your Thoughts so your nervous system has evidence to reference

The Vulnerability Exchange Protocol: Structured Emotional Disclosure
The Vulnerability Exchange Protocol is the operating system that replaces The Exposure Response's default patterns. Instead of Fortress, Flood, or Oscillation, you get a structured decision framework for every disclosure moment.
The protocol has four components:
Component 1: The Pre-Disclosure Check
Before sharing anything at Level 3 or above, run this internal assessment:
1. What level am I about to share at? (Identify the gradient level) 2. What trust evidence supports this level? (List specific behaviors, not feelings about the person) 3. Am I sharing because I want connection, or because I want relief? (Connection-motivated disclosure builds intimacy. Relief-motivated disclosure is emotional dumping that creates obligation, not closeness.) 4. Would I feel safe if this information were used against me? (If no, the trust level isn't high enough for this disclosure.)
The Pre-Disclosure Check takes 30 seconds and prevents the majority of vulnerability miscalibrations I see in my practice. Most premature disclosures happen because people skip straight from impulse to sharing. Adding the check between impulse and action gives your rational brain time to participate.
Component 2: The Reciprocity Monitor
Healthy vulnerability is reciprocal. If you're consistently sharing at a deeper level than the other person, one of three things is happening:
a) They're at a different pace (normal — give time) b) They're not capable of matching your depth (compatibility issue — not fixable) c) They're collecting information without offering equivalent access (exploitation pattern — the same mechanism used in love bombing)
The Reciprocity Monitor tracks the balance over time. I tell clients to notice: after you share something at Level 3, does the other person eventually share at Level 3 too? Not immediately — that would be performative. But within a few interactions, do they match your depth with their own genuine disclosure?
If you're consistently one or two levels deeper than the other person after multiple interactions, the exchange is unbalanced. Either slow your disclosure to match their pace, or directly address the imbalance: "I notice I've been sharing more about my emotional experience than you have. I'd love to know more about yours."
Their response to that direct request is diagnostic. A person who's genuinely at a slower pace will acknowledge it and begin sharing. A person who's collecting will deflect, redirect to you, or offer surface-level responses that sound vulnerable but contain no actual risk.
Component 3: The Disclosure Recovery Window
After any Level 3+ disclosure, your nervous system will activate some version of The Exposure Response — even when the disclosure went well. This is normal. Your system is still calibrated for threat, and it takes time to update.
I call the period after a significant disclosure The Recovery Window: typically 24-48 hours where you may feel exposed, regretful, or anxious regardless of how the other person responded.
During The Recovery Window: - Don't evaluate the disclosure's impact while your nervous system is activated - Don't seek immediate reassurance from the person you disclosed to (this trains your system to need external validation after every opening) - Do journal about what you shared, how it felt, and how it was received — Untangle Your Thoughts is designed for exactly this processing - Do wait until the window closes (48 hours) before assessing whether the disclosure strengthened or weakened the connection
The Recovery Window shrinks over time as your nervous system accumulates evidence that vulnerability can be safe. Early disclosures may produce 48-hour recovery periods. Six months into a healthy connection, the window may be 2-3 hours. This is your system recalibrating — exactly the process you want.
Component 4: The Safety Audit
Every 30 days in a new connection, run a structured review:
- What level have I been sharing at? - What trust evidence has accumulated to support that level? - Has the other person demonstrated care with what I've shared? (Specific behaviors, not feelings) - Has any disclosure been referenced in conflict, used as leverage, or shared with others without permission? - Do I feel more or less safe sharing with this person compared to 30 days ago?
The Safety Audit provides the longitudinal data your nervous system needs to make accurate trust assessments. Without it, you're relying on moment-to-moment emotional impressions that The Exposure Response distorts.
If the audit reveals consistent safety evidence: graduate to the next vulnerability level. If it reveals even one instance of disclosed information being weaponized, used as leverage, or shared without consent: drop back one level and observe for another 30 days before reassessing.
The protocol isn't about restricting vulnerability. It's about making vulnerability sustainable — something you can practice consistently rather than something you attempt dramatically and then withdraw from.
Key Insights: - The Vulnerability Exchange Protocol: four-component system replacing Exposure Response defaults - Pre-Disclosure Check: 30-second assessment preventing the majority of vulnerability miscalibrations - Reciprocity Monitor: tracks whether disclosure balance is healthy or exploitative - The Recovery Window: 24-48 hours of post-disclosure nervous system activation that shrinks over time - Monthly Safety Audit: longitudinal trust data your nervous system can't generate from moment-to-moment impressions
Put It Into Practice: - Run the Pre-Disclosure Check before any Level 3+ sharing — 30 seconds prevents most regretted disclosures - Track reciprocity: if you're consistently 1-2 levels deeper than the other person, slow down or address the imbalance directly - Expect The Recovery Window after significant disclosures — don't evaluate the disclosure during it - Run the Safety Audit every 30 days and let the evidence determine your next vulnerability level
Key Points
- Four protocol components: Pre-Disclosure Check, Reciprocity Monitor, Recovery Window, Safety Audit
- Pre-Disclosure Check: 30-second internal assessment distinguishing connection-seeking from relief-seeking
- Reciprocity Monitor: tracks disclosure balance to identify exploitation patterns
- Recovery Window: 24-48 hour post-disclosure activation period that shrinks as trust evidence accumulates
- Monthly Safety Audit: structured 30-day review providing longitudinal trust data
Practical Insights
- Run the Pre-Disclosure Check before any Level 3+ sharing — it prevents most vulnerability regret
- Monitor reciprocity: consistently sharing 1-2 levels deeper signals imbalance that needs addressing
- Don't evaluate a disclosure during The Recovery Window — wait 48 hours for your nervous system to settle
- Use Untangle Your Thoughts for the monthly Safety Audit — evidence on paper overrides The Exposure Response

When Vulnerability Gets Weaponized: Recognizing Exploitation Patterns
The fear behind The Exposure Response isn't irrational. Some people do use vulnerability against you. Recognizing the specific patterns by which this happens lets you intervene early rather than shutting down entirely.
I've catalogued four Vulnerability Exploitation Patterns from my work with clients who had their emotional disclosures weaponized:
Pattern 1: The Archive They remember everything you share — not to understand you, but to store it. Your fears, insecurities, and past wounds get filed away and deployed during conflict.
How it manifests: During an argument, they reference something you shared in a vulnerable moment. "Well, you said yourself you have trust issues, so maybe this is just your problem." "You told me your dad was like this — are you sure you're not projecting?"
The mechanism: They convert your self-disclosure into an argument against your own perceptions. Your vulnerability becomes evidence that your feelings aren't valid.
Diagnostic marker: Do they reference your disclosed vulnerabilities during disagreements? If intimate information surfaces in conflict contexts, archiving is active.
Pattern 2: The Broadcast They share what you've told them with others — friends, family, social circles — without your consent. Sometimes it's framed as concern: "I'm worried about her, she told me she's been struggling with..." Sometimes it's entertainment or social currency.
How it manifests: You discover that people know things about you that you only shared with your partner. Or their friends reference your personal information in ways that reveal it was discussed.
The mechanism: Your private disclosure gets converted into public information, violating the implicit container of the vulnerability exchange.
Diagnostic marker: Has information you shared privately with this person surfaced in other contexts? Even once is significant — it signals that your disclosures are not held as confidential.
Pattern 3: The Leverage Your vulnerability becomes a tool for controlling your behavior. They use your fears to keep you compliant and your insecurities to maintain power dynamics.
How it manifests: "If you leave, you'll just repeat the same pattern — you said so yourself." "You told me you can't handle being alone. So maybe you should think about that before making demands." They use your own words to argue against your autonomy.
The mechanism: Your self-awareness gets turned into a leash. The more honestly you've shared about your patterns and fears, the more material they have to argue that any boundary you set or change you seek is just "your issues talking."
Diagnostic marker: Do you feel like your disclosures have reduced your power in the relationship? If sharing vulnerabilities leaves you with less agency rather than more connection, leverage is operating.
Pattern 4: The Comparison Mirror They use your disclosures to position themselves as superior or to make you feel grateful for their tolerance of your flaws.
How it manifests: "I accept your anxiety even though it's a lot." "Most people wouldn't be as patient as I am with your trust issues." "I chose to be with you despite everything you've told me about your past."
The mechanism: Your vulnerability gets reframed as a deficit that they're generously tolerating, which creates a debt dynamic. You feel you owe them for their patience with your disclosed struggles.
Diagnostic marker: After sharing vulnerabilities, do you feel indebted to the person rather than closer? Does their response to your disclosures make you feel like a burden rather than understood?
What to Do When You Identify a Pattern:
One instance of any pattern warrants a direct conversation: "When you referenced my anxiety during our argument, it felt like you were using something I shared in trust. That's not okay."
Their response is the data: - Genuine accountability: "You're right. I shouldn't have done that. I won't reference that in conflict." AND subsequent behavioral change. - Deflection: "I was just making a point" / "You're being too sensitive" / "I was trying to help."
If the pattern repeats after a direct conversation: drop your vulnerability level by two grades and restrict future disclosures until trust evidence accumulates at the lower level. This isn't punishment — it's protection. Your vulnerability is your most valuable relational resource. You don't hand it to people who've demonstrated they'll misuse it.
If the pattern is chronic across multiple interactions: this is a fundamental compatibility failure around attachment security. You cannot build safe vulnerability with someone whose system treats your disclosures as ammunition. This isn't fixable through communication — it requires the other person to fundamentally change how they process emotional information.
Key Insights: - Four Vulnerability Exploitation Patterns: Archive (stored for conflict), Broadcast (shared without consent), Leverage (used for control), Comparison Mirror (reframed as deficit) - Each pattern has a specific diagnostic marker that identifies it early - One instance warrants a direct conversation; the response is the data - Repeated exploitation after direct conversation means dropping vulnerability level by two grades - Chronic exploitation is a fundamental compatibility failure, not a communication problem
Put It Into Practice: - Learn the four exploitation patterns so you can name them when they occur — naming is the first step to intervention - After any disclosure, monitor for exploitation markers over the following weeks - One violation plus genuine accountability equals second chance with monitoring - Repeated violation after clear conversation equals permanent vulnerability reduction with that person
Key Points
- Four exploitation patterns: Archive (conflict weapon), Broadcast (privacy violation), Leverage (control tool), Comparison Mirror (deficit framing)
- Each pattern has specific diagnostic markers for early identification
- One instance warrants direct conversation; the response determines next steps
- Repeated exploitation after direct conversation requires dropping vulnerability level by two grades
- Chronic exploitation signals fundamental compatibility failure, not a communication gap
Practical Insights
- Learn the four patterns by name so you can identify them in real-time, not just in retrospect
- Monitor for exploitation markers in the weeks following any significant disclosure
- One violation plus genuine accountability: second chance with monitoring. Repeated violation: permanent reduction.
- If disclosures consistently leave you feeling indebted rather than connected, Comparison Mirror is active

Rebuilding Vulnerability Capacity: The Practice Framework
Vulnerability capacity doesn't rebuild through one dramatic act of openness. It rebuilds through repeated small exposures in safe contexts — the same principle behind exposure therapy for phobias. Your nervous system needs accumulated evidence that opening up doesn't always lead to injury.
I designed The Practice Framework around this principle: graduated vulnerability practice that starts in the safest relationships you have and progressively extends outward as your system accumulates positive evidence.
Phase 1: Safe Base Practice (Weeks 1-4) Practice Level 2-3 vulnerability with people who've already earned high trust: close friends, family members you feel safe with, a therapist. These are relationships where the trust evidence is already established.
Why start here: your nervous system needs to re-learn that vulnerability can be safe before you attempt it in new or unproven relationships. Practicing with trusted people provides the positive data your system needs to begin recalibrating.
Specific exercises: - Share one genuine feeling per week with a trusted friend (not performing fine — actual emotional honesty) - When someone asks how you are, answer truthfully once per week instead of defaulting to "good" - Notice The Recovery Window after each practice disclosure — is it shortening over the weeks?
Phase 2: Graduated Extension (Weeks 5-12) Extend Level 2 practice to newer relationships: recent friends, social acquaintances, colleagues you're building connection with. Keep disclosures at Level 2 (personal context, not emotional depth) and observe responses.
Why this progression matters: you're building a dataset. Your nervous system tracks how each person handles the information you share. Some will handle it with care. Some will be indifferent. Rarely, someone will mishandle it. Each data point updates your system's trust predictions.
Specific exercises: - Share a personal preference or opinion that feels slightly exposed with one newer connection per week - Track how each person handles the disclosure (received, dismissed, referenced appropriately later, ignored) - Use Untangle Your Thoughts to log disclosure outcomes — the pattern over time reveals who earns progression to Level 3
Phase 3: Depth Calibration (Months 3-6) With people who've demonstrated consistent care at Levels 1-2, practice Level 3 disclosure (emotional honesty). This is where the real recalibration happens — your nervous system encounters emotional vulnerability being received safely and begins updating its threat assessment.
Why this is the critical phase: Level 3 is where The Exposure Response fights hardest because it's the first level where exploitation becomes possible. Your system will resist. The Recovery Window may expand temporarily. This is normal — your system is being asked to override a protective program that's been running since the breakup.
Specific exercises: - Share one emotional truth per month with someone who's earned Level 3 trust through demonstrated behavior - After sharing, notice whether you feel closer (safe exchange) or exposed (system still in threat mode) - Run the Pre-Disclosure Check every time until it becomes automatic - Track Recovery Window duration — it should shorten over the months as positive evidence accumulates
Phase 4: Integration (Month 6+) Vulnerability practice begins to feel less like an exercise and more like a capacity. You'll notice you're sharing at appropriate levels without needing to consciously run the protocol. The Exposure Response still activates occasionally — especially with new people or after stressful periods — but it no longer controls your default.
What integration looks like: - You can identify your vulnerability level in real-time without formal assessment - You can gauge trust evidence intuitively (though formal checks remain useful for new relationships) - The Recovery Window after Level 3 disclosures is hours, not days - You can recognize exploitation patterns early and respond without shutting down entirely
The timeline is approximate. Some women move through phases faster, especially with therapeutic support. Others need longer in Phase 1 if the trust violation was severe. The pace doesn't matter. The direction does.
What matters is that you're building evidence — one small disclosure at a time — that your nervous system can use to update its predictions about vulnerability. Not all at once. Not with everyone. Not because someone told you to be brave. Because you've built a system that lets you open up safely, gradually, and in direct proportion to the trust that's been earned.
Key Insights: - Vulnerability capacity rebuilds through graduated small exposures, not dramatic single acts - The Practice Framework: four phases from safe base practice through integration over 6+ months - Safe Base Practice (Phase 1): practice with already-trusted people to give nervous system positive evidence - Graduated Extension (Phase 2): expand Level 2 practice to newer connections, building a trust dataset - Depth Calibration (Phase 3): Level 3 practice where real recalibration happens — system updates threat assessment - Integration (Phase 4): protocol becomes capacity; vulnerability feels natural rather than effortful
Put It Into Practice: - Start Phase 1 this week: share one genuine feeling with a trusted friend instead of defaulting to 'fine' - Track Recovery Window duration after each practice disclosure — shortening windows are progress evidence - Log every disclosure outcome in Untangle Your Thoughts — the pattern over months shows your system recalibrating - Don't rush phases. Phase 1 feeling boring means it's working — your nervous system is building the safety baseline it needs for later phases
Key Points
- Vulnerability capacity rebuilds through repeated small exposures in safe contexts, not dramatic gestures
- Four-phase Practice Framework: Safe Base (weeks 1-4), Graduated Extension (weeks 5-12), Depth Calibration (months 3-6), Integration (month 6+)
- Each phase builds evidence your nervous system uses to update threat predictions about vulnerability
- Recovery Window shortening over time is measurable progress — track it deliberately
- Integration means the protocol becomes automatic capacity, not a conscious exercise
Practical Insights
- Start this week: share one real feeling with a trusted friend instead of performing 'fine'
- Track Recovery Window duration — this is your measurable recalibration metric
- Log disclosure outcomes in Untangle Your Thoughts over months to see your system updating
- Phase 1 feeling boring is the sign it's working — safety baseline needs to feel unremarkable before you progress
Frequently Asked Questions
Why is it so hard to be vulnerable after a breakup?
Your nervous system runs The Exposure Response — a protective shutdown that activates after trust violation. During your relationship, vulnerability was linked to reward (share something, receive connection). When trust was violated, that circuit reversed: vulnerability now signals threat. The racing heart when conversations get personal, the deflection, the performing 'fine' — these are protective reflexes, not personality flaws. They require a structured protocol to redirect, not just willpower to override.
How do I open up to someone new without getting hurt again?
Use The Vulnerability Gradient: five levels of disclosure calibrated to demonstrated trust evidence. Share at Level 1-2 (preferences, background) early on, progressing to Level 3 (emotional honesty) only after the other person has demonstrated consistent respect, reliability, and appropriate handling of earlier disclosures. The Gradient Rule: never share at a level higher than the trust evidence supports. Depth without evidence is exposure, not intimacy.
What is the difference between healthy vulnerability and oversharing?
Healthy vulnerability is calibrated — the depth of sharing matches the trust the other person has demonstrated through behavior. Oversharing (the Flood pattern) is disclosure driven by relief-seeking rather than connection-building, typically at Level 3-4 depth with Level 1 trust. The Pre-Disclosure Check distinguishes them: ask whether you're sharing because you want connection (healthy) or because you want relief from carrying it alone (oversharing). Relief-seeking creates obligation, not closeness.
How do I know if someone is safe to be vulnerable with?
Track Graduation Markers — specific behavioral evidence at each vulnerability level. Level 1 to 2: they show up consistently, keep plans, communicate reliably. Level 2 to 3: they've received personal information without judgment, reference it showing they listened, don't use it competitively. Level 3 to 4: they've handled emotional honesty with care, repaired when they've hurt you, shared reciprocally. The evidence accumulates over weeks and months, not days.
How long does it take to rebuild vulnerability after a toxic relationship?
The Practice Framework spans approximately 6+ months across four phases: Safe Base Practice (weeks 1-4, practicing with already-trusted people), Graduated Extension (weeks 5-12, extending to newer connections), Depth Calibration (months 3-6, Level 3 practice where real recalibration happens), and Integration (month 6+, protocol becomes automatic capacity). The pace varies — severe trust violations may require longer Phase 1 practice. Track your Recovery Window duration as your progress metric.
What are signs that someone is using my vulnerability against me?
Four Vulnerability Exploitation Patterns: The Archive (storing disclosures for use in conflict — 'You said yourself you have trust issues'), The Broadcast (sharing private information without consent), The Leverage (using your fears to control your behavior — 'You know you can't handle being alone'), and The Comparison Mirror (reframing your disclosures as deficits they generously tolerate). One instance warrants a direct conversation. Repeated exploitation after clear conversation means dropping your vulnerability level by two grades.
Is it normal to regret being vulnerable even when it goes well?
Yes — this is The Recovery Window. After any Level 3+ disclosure, your nervous system activates some version of The Exposure Response regardless of how the other person responded. The system is still calibrated for threat and needs time to process. The window typically lasts 24-48 hours early in recalibration and shortens over time as positive evidence accumulates. Don't evaluate the disclosure during the window — wait 48 hours before assessing whether it strengthened or weakened the connection.
How do I stop being a people-pleaser and set vulnerability boundaries?
People-pleasing and vulnerability collapse often share the same root: prioritizing the other person's comfort over your own safety. The Vulnerability Exchange Protocol addresses this through the Pre-Disclosure Check (am I sharing for connection or to please?), the Reciprocity Monitor (am I consistently deeper than them?), and the Gradient Rule (never share at a level the trust evidence doesn't support). Start by practicing with Level 2 boundaries: share a genuine preference that might not match theirs, and observe whether they accept it or pressure you to change it.
Conclusion
Vulnerability after a breakup isn't about courage. It's about structure.Your nervous system locked down for a reason — someone used your openness against you. The Exposure Response that resulted isn't something to fight. It's something to redirect through a system that protects you while gradually rebuilding the connections you need.The Vulnerability Exchange Protocol gives you that system: The Vulnerability Gradient tells you how deep to go. The Pre-Disclosure Check prevents impulsive oversharing. The Reciprocity Monitor ensures the exchange is balanced. The Recovery Window gives your nervous system time to process. The Safety Audit provides the evidence your brain needs to update its threat assessment.And if someone does exploit what you share — you now have the four exploitation patterns named and the framework to intervene before the damage compounds.Start where it's safe. Practice at the level that matches the trust that's been earned. Track your Recovery Window and watch it shorten as positive evidence accumulates. Use Untangle Your Thoughts to keep the data your nervous system can't hold on its own.You don't need to tear down the wall. You need to install a door — one you control, that opens at the pace the evidence supports.